App shielding is now part of the baseline for organizations that are serious about mobile app security. If your app handles payments, identity, regulated data, or high-value business logic, you need more than perimeter controls, application-layer proxies, gateways, firewalls, and secure coding. You need protection inside the app itself. That means runtime protection, code obfuscation, and resilience to hold up when the app is running on a hostile device or under active analysis, especially now with AI-enhanced deobfuscation capabilities.
But app shielding still has an operating problem.
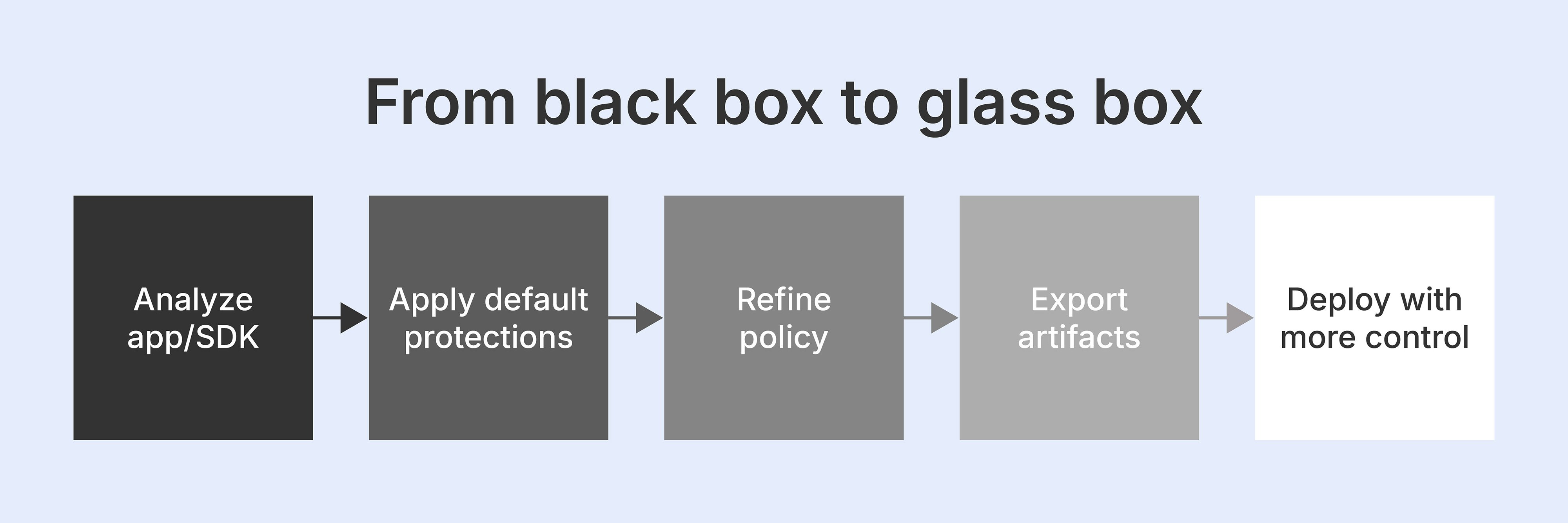
For many teams, it feels like a black box. The protection is there, but it is hard to see, hard to explain, and hard to repeat at scale. That opacity is partly intentional. The internal mechanics of runtime protection and code obfuscation are abstracted so attackers cannot easily reverse engineer the controls and build bypasses. From a security standpoint, that makes sense. From an operational standpoint, it creates friction between security and application teams, and between compliance leads and regulators.
When shielding stays opaque, teams struggle to answer basic questions. What protections are being applied? How does it map to risk? Can we prove best practices are in place? Can we repeat the same process cleanly across release cycles or for other applications? Can non-specialist stakeholders understand what they are buying or approving?
These questions now matter more because app shielding is moving from specialist practice to broader adoption. This is especially the case in regulated environments where proof of protection carries more weight. That is the problem Promon Shield Studio is built to solve.
Read more: App shielding: The essential layer for mobile app security
Why black-box shielding slows teams down
A black box is more than a technical concept. It has rapidly turned into a business problem in application shielding across industries.
If shielding depends on a small group of experts, every evaluation takes high effort. Sales engineers spend more time translating technical value. Buyers who want to “see something” receive command lines, logs, and explanations that do not travel well outside engineering. Internal teams find it harder to show consistency, prove repeatability, and connect protection choices to compliance or business risk. While proven and robust, this approach is not conducive to highly collaborate development teams or AI-enhanced analysis.
The result is slower evaluations, more friction in customer conversations, and weaker time-to-value. With app shielding becoming more critical, protection needs to be transparent and proven across security architects, security and risk management leaders, compliance leads, and even line of business owners, in addition to developers who are typically tasked with embedding security into apps and SDKs post-compile.
There is also a delivery issue. Application hardening through runtime protection and code obfuscation has the most impact when it is applied consistently across every release path that ships to users. If the workflow is too manual, consistency suffers. Small errors in configuration files or missed warnings about unprotected code can lead to serious exposures. That is where strong security can still become operational drag.
Why post-compile protection still matters
Promon’s model starts from a practical advantage. Post-compile app shielding lets teams apply protection without changing source code. That matters because mobile security controls need to fit the way teams ship software, not force a redesign of the build and release process. Post-compile deployment supports rapid rollout, lowers coordination overhead, and makes it easier to fit security into existing delivery paths.
Read more: Secure by design: How SDK teams can protect code without compromising speed
This is not only about convenience. It is about operational efficiency. If protection can be applied later in the release cycle, with less disruption and less dependency on source-level changes, it becomes easier to standardize and scale. Especially with a hybrid approach that balances effectiveness and deployment velocity. That is one of the reasons app shielding is valuable for both mature development teams and organizations trying to improve control without slowing delivery.
What app shielding is protecting
At a technical level, app shielding addresses the threats that show up once the app or SDK is released into the wild.
Runtime protection for hostile environments
Mobile apps run on endpoints you do not control. Your SDKs run in partner apps you have limited control over. Devices may be rooted, instrumented via debuggers or hooking frameworks, infected with malware, emulated, or manipulated at runtime. Runtime protection helps the app detect and respond to those conditions while it is running. That matters for anti-tampering, fraud prevention, and maintaining integrity in the face of increasingly sophisticated attackers.
Read more: What is RASP and how does it secure web apps vs. mobile apps?
Code obfuscation for IP and attack resistance
Code obfuscation protects a different part of the problem. It raises the cost of reverse engineering. It makes sensitive routines, business logic, and proprietary implementation details harder to inspect, copy, and alter. For teams shipping valuable business logic or reusable components, obfuscation is part of protecting intellectual property as well as reducing attacker understanding of the app’s internal design. In many cases, this sensitive code is the business logic that directly leads to revenue, or if bypassed, losses.
Read more: Obfuscation explained: A comprehensive guide to code protection techniques
Together, these controls help keep apps, users, and data safer from tampering, reverse engineering, fraud, and attempts to bypass critical security controls.
Protecting a mobile app is not the same as protecting an SDK
A homegrown banking app gives you end-to-end control over the app, its release path, and its user flows. A biometric SDK embedded in another vendor’s app is different. The security requirement may be just as high, but your control surface is narrower, and the runtime context is not fully yours. The same pattern shows elsewhere. Protecting a new game client from tampering is not the same as protecting marketplace logic from cheating or entitlement bypass. Same discipline, different constraints.
That is why shielding decisions need more than raw technical power. They need context, policy control, and a workflow that helps teams apply the right protection to the right asset. But the risks are the same. Whether you are the SDK provider or the app owner leveraging a third-party integration, you are subject to the same scrutiny and potential fallout from any security incident.
What Shield Studio changes
Promon Shield Studio offers a guided app shielding experience in a modern interface. The same always-on protection, now with greater visibility and deployment velocity. This move from black-box to glass-box allows customers to be more informed, in control, more collaborative, and able to take advantage of AI-enhanced analysis.
That does not mean exposing security internals in a way that weakens protection. It means making the shielding process easier to inspect, configure, and operationalize. Shield maintains the protection depth. Studio improves how teams deliver its impact.
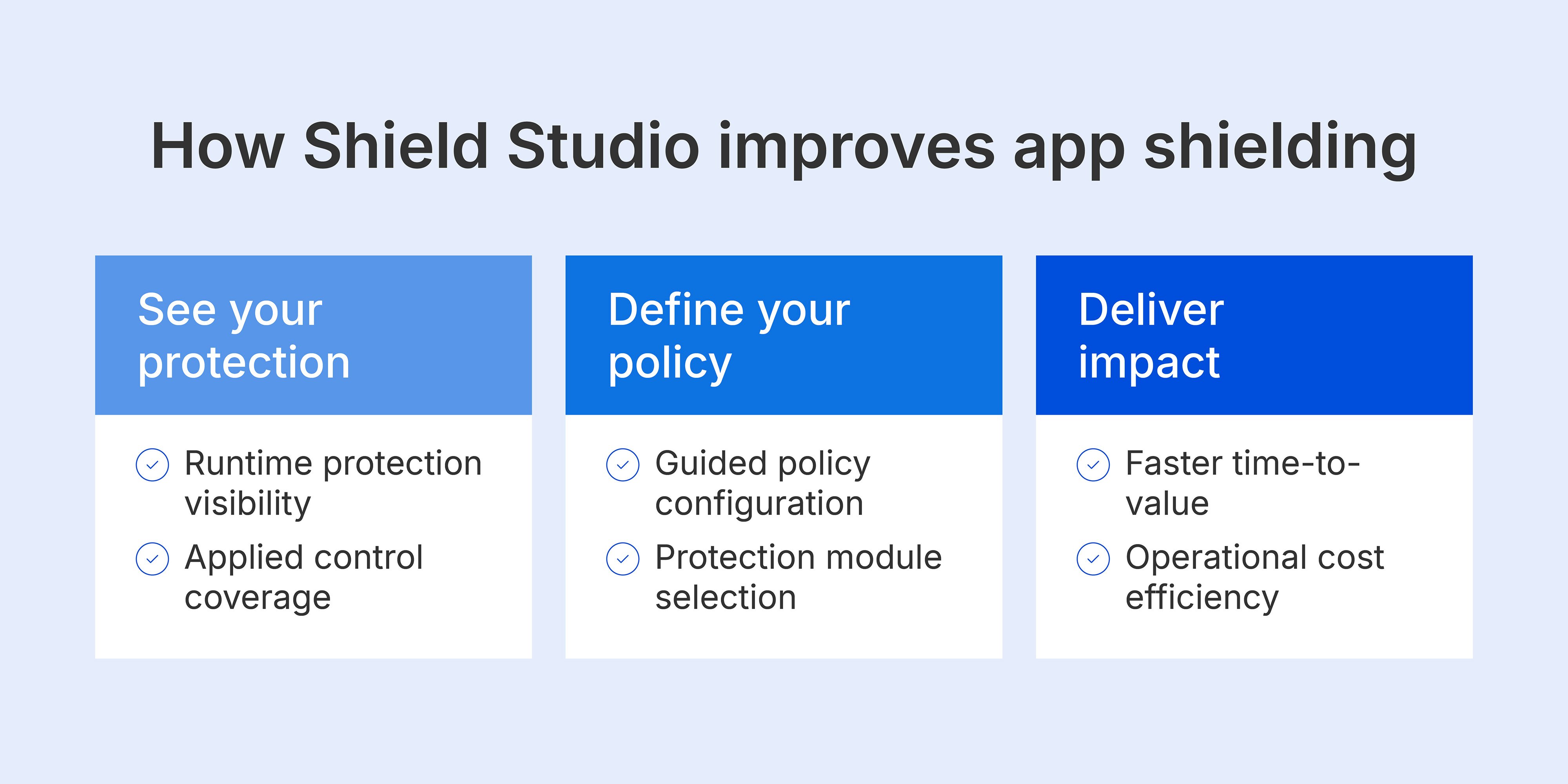
See your protection
Visibility is not merely a technical benefit. It is a business imperative for organizations that are serious about application security. Developers appreciate tools that integrate within their frameworks and CI/CD pipelines, but security teams want to verify protections, ensure alignment to best practices, and may need to show proof to auditors or business partners.
Shield Studio gives users a clearer view into the shielding process and the protections being applied, while optimizing deployments using expert analysis and best practices. That helps technical teams prove their security posture. It also helps security architects, risk leaders, and business stakeholders understand what they are evaluating. When buyers want proof, transparency matters. Shield Studio provides visible protection and transparent runtime security.
Read more: Protection is not intelligence: Why blocking mobile threats is no longer enough
Define your policy
Shield Studio is built to guide configurations as well as provide best practices for customizing them.
It analyzes underlying binaries and exposed functions, applies default configurations for detections and obfuscation, and guides users toward the modules and tools that fit what the application can protect. Teams can also bring in customized configurations based on previous projects or proven deployments. This reduces manual setup, limits operator error, and gives users a stronger path from baseline defaults to app-specific policy tuning.
Deliver impact
The immediate and obvious benefit is a better experience. But the more significant benefit is a tighter operating model.
Studio supports drag-and-drop upload for apps and SDKs, exports key artifacts such as protected outputs, mapping files, logs, and JSON configuration files, and manages applications and configurations as projects. That helps with change control, repeatability, and cleaner handoff between teams. It also fits naturally into delivery and operational pipelines with less overload across tooling and workflows. This customer-controlled, expert-guided approach is designed for seamless deployment.
That is where the technical and business values meet. Better workflows translate to less friction across teams. Improved visibility means less friction in audits. Better repeatability means stronger governance and more consistent security outcomes.
A clearer path to mobile app security
App shielding should not stay trapped inside a black box. Teams need strong runtime protection and code obfuscation, but they also need a way to apply those controls consistently, explain them clearly, and scale them across apps and SDKs without creating delivery drag.
That is the role of Promon Shield Studio. It helps teams apply shielding with more visibility, more control, and less operational friction. Security teams get a more structured way to configure and scale protection across apps and SDKs. Business stakeholders get a clearer view of what is in place and why it matters. The result is stronger mobile app security that is easier to operationalize, easier to validate, and easier to put to work across the software delivery lifecycle.
Promon Shield Studio. Defined by you. Guided by us. Enforced by Shield.







